Schedule
The 2k24 program
-
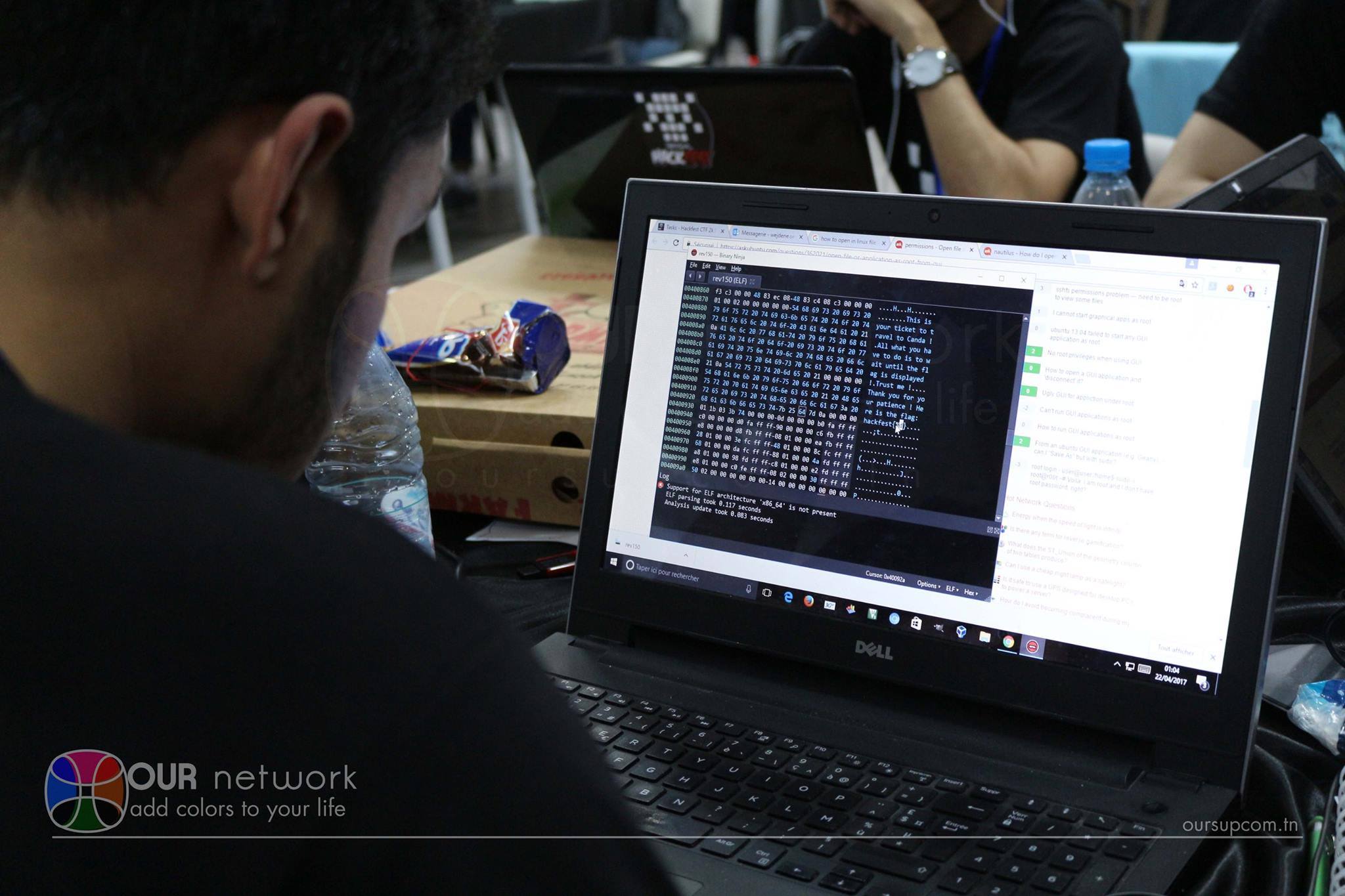
CTF Qualification Round
The CTF Qualification Round is an online event lasting 18 hours, where registered players compete to solve challenges across various categories. Top 60 contestants proceed to the Final Round.
- Online
- FREE
-

CTF Final Round
The CTF Final Round is a 12-hour on-site competition where selected contestants compete in teams. Held overnight, the competition fosters a distraction-free environment for hackers to focus and collaborate.
-
Conferences and Workshops
This year's edition will feature multiple conferences and in the theme of Cloud security, you can visit our Facebook page to learn more about our speakers.
- ElGazala Technopark
- FREE
-
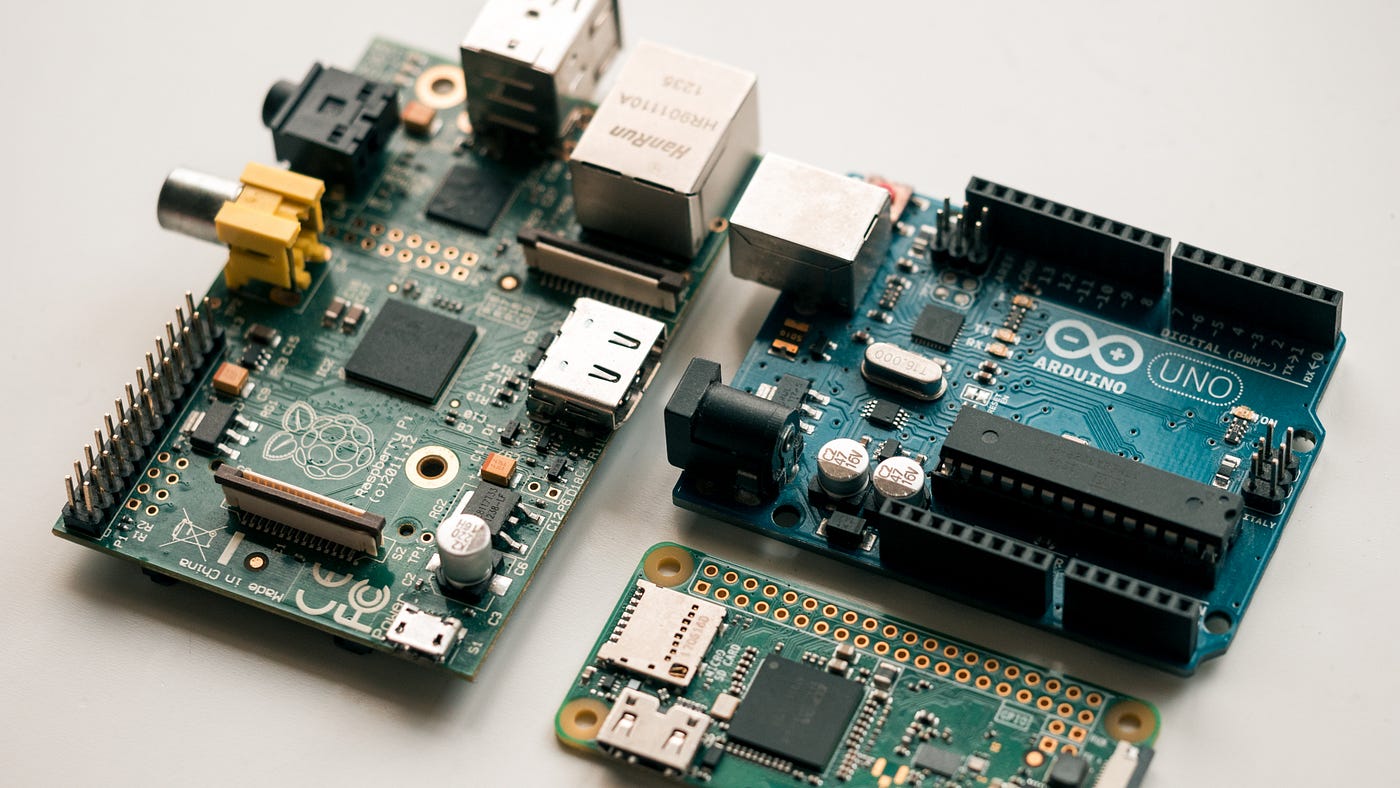
IOT hacking Challenges
Conquer cybersecurity challenges, from analyzing Arduino firmware to exploiting binary program vulnerabilities. Join teams, outsmart opponents, and showcase your hacking skills in this thrilling competition!
- ElGazala Technopark
- FREE
-

Crypto Kids Workshop
Explore secret codes and ciphers in a fun, interactive setting! Ignite curiosity with our engaging cryptography session for kids.
- ElGazala Technopark
- FREE